Security Initiatives
The IT Security and Identity Management (ITSEC) team is always striving to increase campus network and data security. Listed below are our upcoming security initiatives:
Email Protection
In 2020, Microsoft will disable Basic Authentication (e.g. IMAP/POP) for Office 365 to address security concerns. Basic Authentication means that the client application passes the username and password with every request, which makes it easier for attackers to capture a user's credentials. Beginning on January 31, 2020, ITS will begin making configuration changes to improve Microsoft Office 365 email security. Frequently Asked Questions regarding this change.
Malicious Website Protection
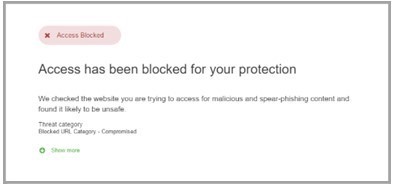
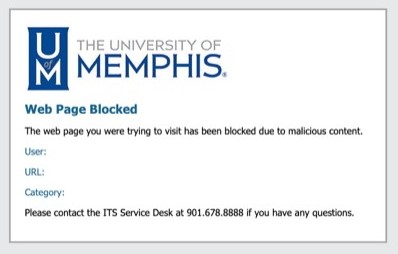
The protections described below are built-in to make our internet experiences safer. If you encounter either of the following messages, it does not necessarily mean that your computer has been infected or compromised, it could simply mean that your browser settings need to be adjusted. If you get either of these messages while trying to access a website that you know is safe, please contact the Service Desk at 901.678.8888 for assistance.
Website Link Protection
This service limits access to known sites that deliver malware, attempt to steal credentials or are associated with known phishing campaigns. If users attempt to access such a site, they will be redirected to a page indicating the content is unavailable.
Email Link Protection
This service protects links in email messages, including those found in attachments. A check is performed when users click on a link or an attachment from an email message, scanning for potentially malicious content. If the content is determined to be unsafe, users will be redirected to a page indicating the content is unavailable.